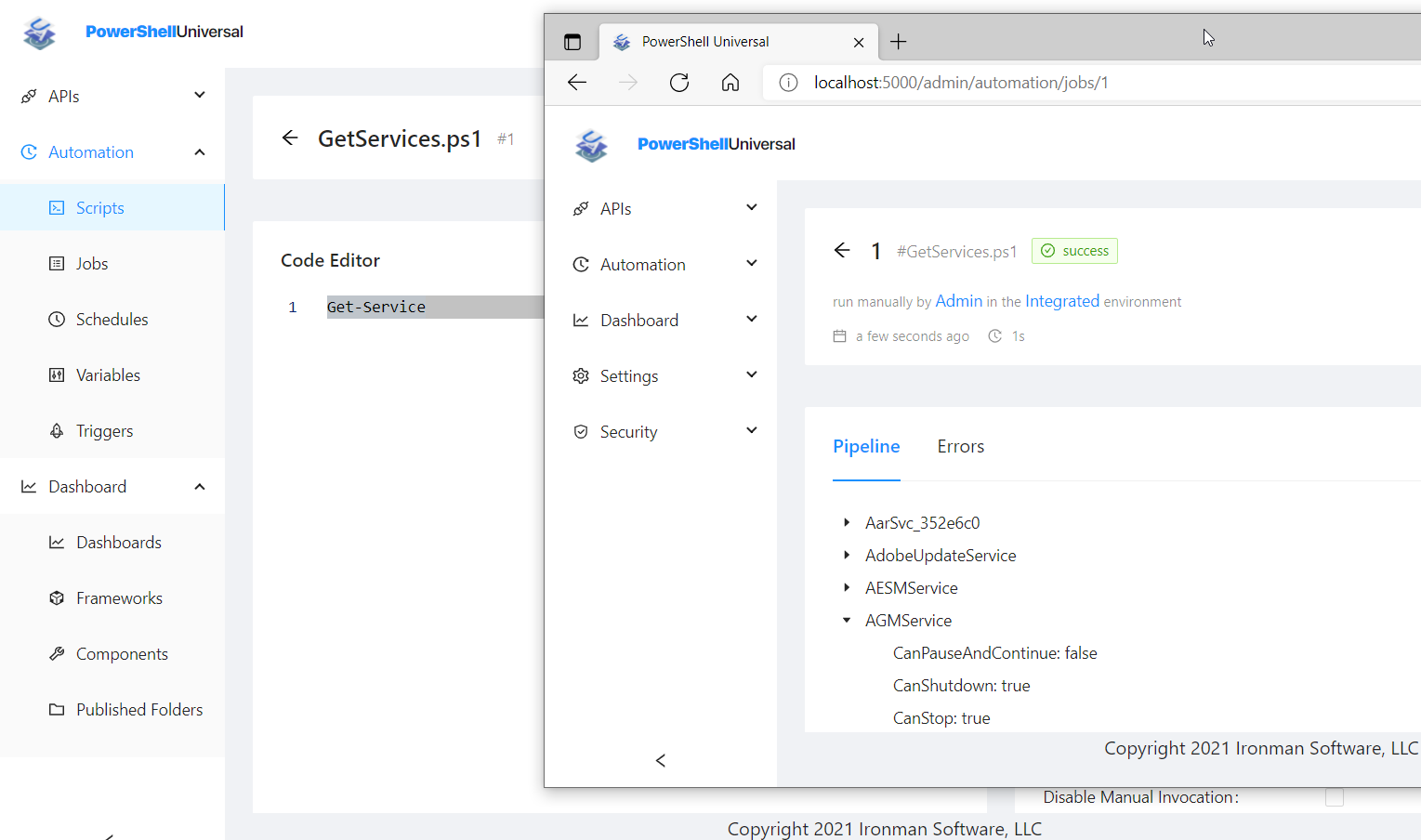
Ensure your system is accessible by exposing your scripts as REST APIs. Host your scripts in a web interface for ad-hoc execution or robust scheduling. Build custom web-based tools to enable your users to handle tasks themselves without elevated credentials or opening support tickets. Enforce role-based access controls and secruity requirements across the entire platform.
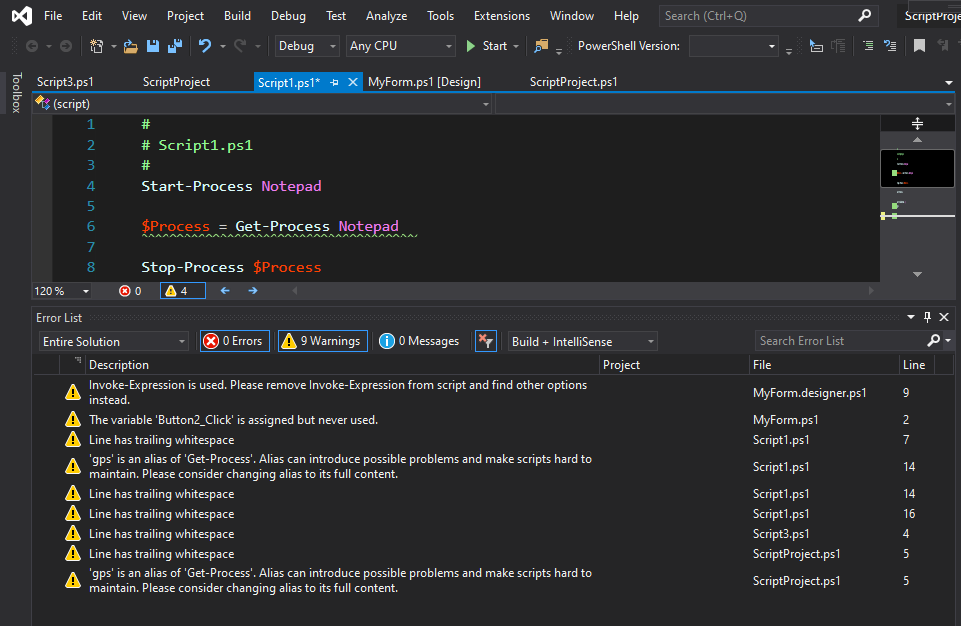
Enhance your favorite editor like Visual Studio or Visual Studio Code with extensions that make scripting easier, faster and more productive. Alternatively, keep things simple with an editor built for PowerShell. Protect your desktop with and from PowerShell.
Whether you're a small business or a large enterprise, you will be in good company among the customers using our solutions. With millions of installs, API requests, and scripts executed every month, we help ensure you can make the most of your IT team.










PowerShell Universal uses JSON Web Tokens to allow for access to APIs within the system. It makes it easy to issue app tokens and control them directly within the platform. That said, JWT is a standard technology, and you may want to use tokens issued by other authorization servers. In this post, we’ll look at how to use Okta tokens with PowerShell Universal. Configuring Okta First, we’ll need to register an app within Okta so we can grant tokens.
PowerShell Universal has evolved immensely over the years. At first, we exposed REST APIs for all our cmdlets. Each cmdlet would simply call a REST API and return data. Then, we had users that wished to call the cmdlets without having to provision app tokens. This led to cmdlets the could run over our internal gRPC channel as well as directly via our integrated environment. This led to a lot of complexity.
Today, we are happy to announce the third beta of PowerShell Universal v5. Information about the previous betas can be found here: v5 Beta1 v5 Beta2 You can download the latest version of PowerShell Universal from our website. Download Now Permissions We’ve added granular permissions to PowerShell Universal. This replaces the previous access control system and builds onto existing role-based access. Permissions can be assigned to identities and roles to control access to specific features of PowerShell Universal.